Ransomware…! The thing hitting the news these days. Almost a month ago, half of the world was hit by the dirty WannaCry and now it’s the time of Petya. Petya Ransomware is not the newest product in the market of Cyber Threats. This danger is quite old and was identified already almost a year ago. There are still different opinions about whether the recent Cyber Attack was a Petya Ransomware or not. Some called it Petya, some called NotPetya, and some experts are even saying it’s not even a ransomware, just a data wiper, but the fact is that it has behaviour almost similar to the old Petya Ransomware. So I decided to write about the behaviour of the old and still alive Petya Ransomware as this possesses a completely different and more dangerous approach towards destruction of the system.
-
Petya- A Different Way of Destruction
Most of us became aware about ransomwares recently only after the dirty WannaCry shook the world. The common thinking about any encryption ransomware is that they encrypt the files on the system one by one while the system is in processing. That’s how most of the ransomwares work, they simply encrypt your files and lock you out. But Petya is different, it does not encrypt your files the normal way while your system is Powered ON and processing, It does a low level encryption at the time Booting.
-
Petya, has it’s own Boot Loader and even a Kernel
Yes, you read the heading correct, Petya is not as simple as WannaCry, but more complex equipped with weapons like an own boot Loader and a Kernel. Instead of encrypting files one by one, it denies access to the full system by attacking low-level structures on the disk. Once the ransomware files are dropped, Petya is configured to execute at the next boot and install it’s own boot loader. The affected system’s master boot record (MBR) is overwritten by Petya’s boot loader and a tiny malicious kernel is written. Then, this kernel proceeds with further encryption.
-
Petya doesn’t encrypt files
The Other behavioural phenomena of Petya is that it does not truly encrypt all the files on the hard disk. Though it’s ransom note says it has encrypted all files, but it doesn’t. It encrypts the Master File Table (MFT) making the whole disk unreadable. As Malwarebytes states, we can see many valid strings in the disk affected by Petya using forensic tools. So at an early stage, it is possible to prevent the loss of our data by simply not letting our system boot.
-
Petya – Step by step behaviour Analysis
We understand, Petya is complicated and has very different approach. Here is a step by step behaviour Analysis of Petya Ransomware
- The victim receives the Malicious Files through many ways including Email Attachments, remote Desktop Connections (or tools), File Sharing Service, Infected File Downloads from unknown sources, infected free or cracked tools etc.
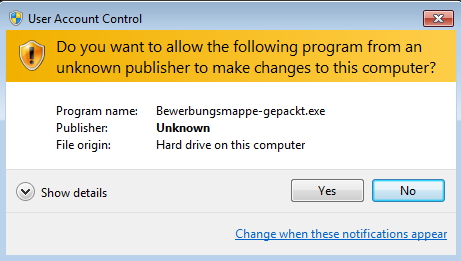
- As soon as the dropper i.e. the malicious executable executes, It asks for UAC (User Account Control) permission as it needs to perform malicious activity.
- Till this stage, our data is safe, and nothing drastic has happened. The disk is still recoverable from the infection as only the beginning of the disk is encrypted. It then overwrites the beginning of the disk and the MBR (Master Boot Record). It makes an encrypted copy of it.
- To process completely, Petya needs the system to be booted. So it forcefully generates a Blue Screen of Death (BSOD). This way it restarts the system in the booting process.
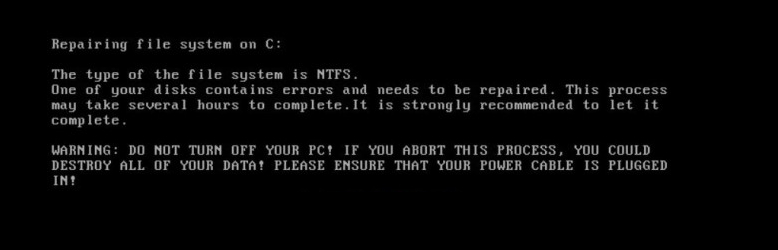
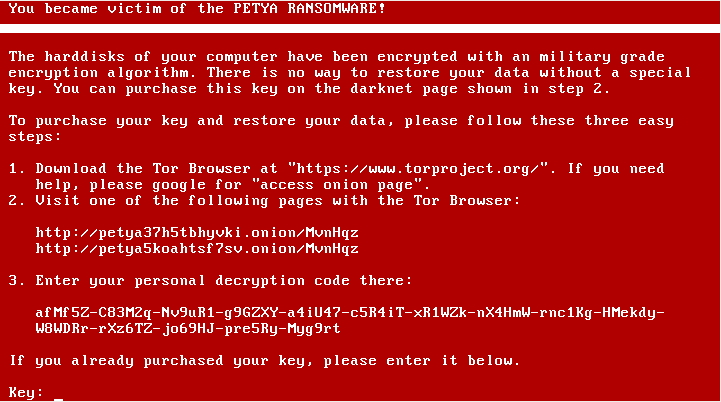
- After this it generates a dummy CHKDSK Scan on the system. And it soon starts showing the Warning Screen or It’s Ransom Note. This note tells the victim about the lock out and asks for a Ransom.
-
Petya Specific Prevention
As we know the execution behaviour of Petya Ransomware, we can consider a preventive measures specific to Petya Ransomware. As Petya needs to boot for its full operation, we can consider disabling Automatic Restarting of our system, which will prevent automatic booting of infected system and Petya will not be able to install a new Boot Loader. We must remember, if we suspect the BSOD is due to infection from Petya, we should never Turn It ON again.
There is a Key here! we should not let Petya boot, if we let it boot, our disk is gone. What we can do instead? Power Off our system permanently! We can recover our data by mounting our disk to another machine (Preferably Linux). There are many other ways which can help recover data from Petya Infected disk. More Information can be found here
Understanding the execution of crime is always necessary to stop the crime. If we can understand the execution of Cyber Attacks, we can take preventive steps. With few easy steps we can combat Petya or any other Cyber Attack and prevent it from reaching it’s goal.